Anti-Phishing Solution and awareness in the Corporate and Banking sectors

Introduction
A phishing email is a serious matter. 91% of all cyberattacks start with phishing emails. Taking actions to protect against phishing attacks is the most important aspect now, with a robust and intelligent solution. This article will help you understand the overview, challenges, solution, and plan strategy.
Overview about the challenge of phishing scams attacks in the Banking and corporate sector. Several highly successful cyber threats are based on phishing techniques. In broad, phishing is utilized to exploit banking credentials for stealing, either directly, via spoof sites, and utilizing installed malware. Some examples incorporated with these below factors:
Bank-Targeted Phishing
Spear phishing, an alternative to phishing, is an intensely thriving method established on social engineering. That is based on manipulating human behaviour and particularly targeting a known user. Bank phishing attempts mainly concentrated on staff such as IT administration staff. Employees target a spear-phishing attack in the finance sector, the most targeted enterprise.
Customer-Targeted Phishing–Companies
Many organizations are getting targeted via a strategy called ‘Business Email Scams’ or BES. The email usually has a critical request to share money with a bank account (the cybercriminal holds that). It highly spreads a BES threat; the cybercriminal takes time to know their victim and whom they supply with social engineering schemes to mislead employees of a business into believing they have received an email from a high-level leader, such as a CEO or CFO.
And using this scheme and technique, they are already able to achieve it. Recently, USA-based FBI Bank has warned about this customer target phishing scheme to their users.
Customer-Targeted Phishing – Individuals
In this customer, targeted phishing attackers are more focused and target mobile banking with malware, particularly written to manipulate mobile banking users.
It is a remarkably sophisticated phishing technique called “Android fake login.” It is easily operated and performs by discovering which mobile banking app an individual is using. Then they spread the spoof interface, which detects the user’s login credentials once they enter on the spoof page.
‘Smishing’ is the latest phishing that includes a text message with web links to a spoof site. Attackers intercommunicate this with the bank site, which requests login credentials to the mobile users. As banking sectors are crucial sectors, they send the text message to customers for valuable communications to the users, and they request to send instant bank transactions using mobile apps. Solution of Firewall Protection against Phishing Scams.
How to stay up to date on a phishing scam
Fortunately, there are methods to avoid this situation to overcome the cyber phishing scam. Here we have the guidelines it can help the organization and end-users. These guidelines make users aware so that they can be more alert and follow the basic rules.
Think Before You Click! :
The user must understand what are they trusted or untrusted sites. Hence, before clicking on undesirable web links or any instant messages and random emails, they should ensure what to click and open or not. A phishing email may declare to be from a legitimate business, and when the user clicks the link to the website, it may look. They may seem like it is a genuine website, and an email may request you to fill in the details, but the email may not include the username. Most phishing emails usually start with “Dear Customer,” so according to that, a user should be alert when they come across such type of emails. Instead of clicking on a dangerous link, they can go straight to the source and report to a phishing alarm.
Install an Anti-Phishing Toolbar:
Here we have a mechanism, an Anti-Phishing Toolbar, which is most prominent and customizable on various Internet browsers. These toolbars can be usable on the sites while visiting the page; they can be secure. As it is free, users can plug into their browsers and have a more secure experience. We can consider it is a more protected layer against phishing scams.
Confirm a Site’s Security:
In this secure solution, method users should be more focused on providing sensitive financial data online. They should follow the secure techniques using the fundamental understanding such as the website’s URL should begin with “HTTPS.” There must be a closed lock icon close the address bar. They should ensure the website’s security certificate. If they receive any malicious files, they do not need to open the website and download files from suspicious emails or websites. Sometimes search engines may contain specific links which may reach the users from a phishing webpage, such as offering low-cost products. If a user makes purchases at such a website, cyber criminals can access their credit card details.
Use Firewalls:
High-quality firewalls perform as buffers between the user and system and external intruders. Users must use two additional kinds: a desktop firewall and a network firewall. The desktop firewall is a kind of software, and the network firewall option is a kind of hardware.
When we use them together, they drastically decrease the chances of hackers and phishers entering your computer or network.
Use Antivirus Software:
There are several reasons to use antivirus software included with Unique signatures antivirus software guards as users. We need to make sure their software should be up to date. Anti-spyware and firewall configurable settings should control phishing attacks, and users should modernize the programs regularly.
Firewall protection controls access to malicious and irrelevant files by blocking the attacks. Antivirus software inspects each file that arrives through the Internet to the user’s system. It enables the user to prevent harm to your system. With the help of the latest updated antivirus software, users no need to fear phishing scams.
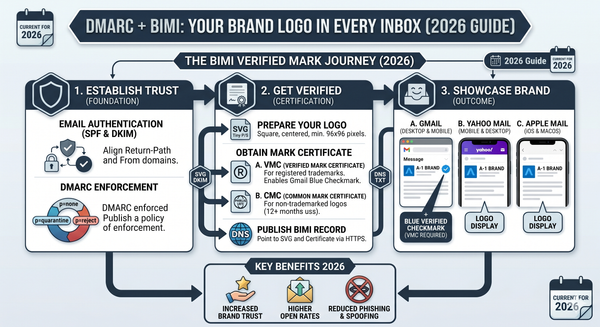
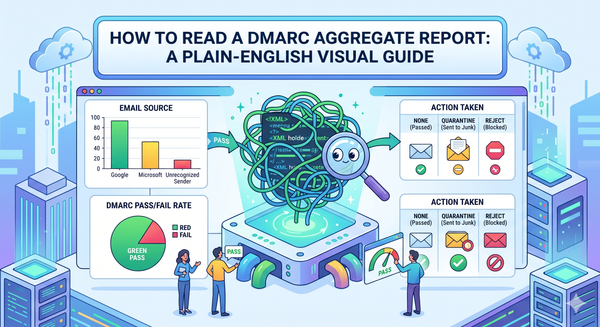
Strategy and plan and resolution from SimpleDMARC for securing emails and brands from their services. DMARC provides the best-advanced threat strategy plan to solve these types of phishing attacks
Link protection:
This solution does not allow users to click on suspicious links as phishing emails won’t reach the user’s email inboxes. Using this can protect every email in real-time-based techniques.
● It also protects confidential data and more extensive corporate networks from phishing attacks.
● Each time a user gets an email with a suspicious link delivered to the users’ inbox that looks like phishing, the system administrator can get the alert and notify them that they can know this and troubleshoot and fix it.
● This assertive level of scanning and monitoring is the best way to protect users from both direct and delayed attacks.
Protect your computer by utilizing security software.
DMARC suggests the rule to set up your software to update automatically so it can handle any unknown security threats.
Secure your mobile phone by specifying software to update automatically. DMARC suggests these important updates could protect the user against security threats.
Watch your accounts by utilizing multi-factor authentication:
Some accounts suggest additional protection by directing two or more credentials to log in to the user account. We can consider it as multi-factor authentication. These credentials users need to log in to your account comes into two categories:
● Something users have: A passcode user gets through an authentication app or a security key.
● Something users are A scan of the user’s fingerprint, eyes retina, or face.
● Multi-factor authentication makes it more formidable for scammers to log in to user accounts to acquire a username and password.
Protect your data by backing it up. Users can copy computer files to external cloud storage hard drives or smartphones. DMRC provides the guidelines to back up your data and ensure these backups aren’t related and connected to the user’s home network.
Intelligent Cybersecurity Awareness Training
DMARC provides training for the employees who experienced phishing attacks in their organization or banking sectors for the standard cybersecurity awareness training services.
They connect Phish Threat email to check the users who have been faced or blocked from visiting a website because of its risk profile and provide the best solutions.
How to train employees on Email Phishing scam
● Keep the employee informed About Phishing Techniques: Users must know the latest invention of phishing scams. For IT administrators, continuous security awareness training and simulated phishing for all users are highly suggested in maintaining security top of mindset throughout the organization.
● Check Online Accounts Regularly: This is a good practice for checking online accounts regularly and changing your passwords. To protect bank phishing and credit card phishing scams, a user should privately check their statements as regularly. They should check their monthly statements of financial accounts and scan every entry carefully to confirm it has made no dishonest transactions without their learning.
● Keep Browser Up to Date: Security patches are regularly released from many browsers as per the defined time. They are helpful for an overcome phishing attacks and making websites more secure. Sometimes we may ignore them, but we should practice updating the browsers. It just takes a minute to update, download and install it.
● Be Cautious of Pop-Ups: Users also need to be cautious of irrelevant Pop-up windows that frequently come when they visit the website and force them to click or open it. We can consider this as also phishing attempts. Many popular browsers inbuilt customizable settings allow users to permit block pop-ups. Using this, users can easily block unrelated pop-ups and allow only relevant ones.
● Never Give Out Confidential Information: As a common rule and understanding, a user should not transmit personal or financially prudent information over the Internet. It is the most important rule we should follow in our daily routine. Many phishing emails will lead you to pages where entries for financial or personal information are needed, and it will force users to enter their information. To protect this, users should not make confidential entries via the links delivered in the emails. They should not send an email with sensitive data to anyone. As a user, they need to make it a practice to match the website’s address. As per the secure website standard, it starts with “HTTPS”.
Conclusion
We hope this article helped you understand the Anti-Phishing Solution. Here we understood the challenges and solutions and how to train employees from the corporate and banking sectors with the best strategy plans of email protection. This article will be helpful to professional developers from the cyber-security and application security teams. You will find these blogs and content in the DMARC community from SimpleDMARC.