Phish, Blow Phish and No Phish
Dive into the Intricacies of Phishing Attacks: Phish, Blow Phish, and No Phish. Discover How Cybercriminals Utilize These Tactics and Implement Robust Security Measures to Protect Yourself and Your Organization from Potentially Damaging Online Scams.

Phish+ing – Phishing Be Aware of this.
Phishing is a form of fraud attack where attackers masquerade as authenticated sender to trick the receiver into believing it is real communication and steal the user’s confidential information such as login credentials, card details, etc. An attacker tricks users into opening malicious links or install some RATs or Malwares, which can be further leveraged to attack the user’s system. Most of the phishing attacks are executed over E-mails. The attackers, in general, send a large number of e-mails. If a small percentage of people also fall for this and give out their confidential information, then attackers important information that would help them in the bigger attacker.
Phishing is a Social Engineering Attack where an attacker finds a way to trick users by sending them e-mails that looks legitimate as real e-mails with some unnoticeable difference which is quite hard for ordinary users to identify.
The attackers use the victim’s information to trick them into falling for the phishing attack by user-targeted Phishing. For example, an attacker would be sending fake offers or security e-mails like changing passwords, easily fooling the user into falling for the attack.
In some cases, attackers use the real domains of the organizations to send the e-mails to the users. This kind of phishing attack is much effective as the user will not think as if it’s a malicious
activity as the mail received is from the real domain from the organization where it’s supposed to be from, and this will easily trick the users into believing it’s an authentic mail. The attack executes successfully for an attacker.
Blow Phish – Different Type of Phishing Attacks
There are different kinds of Phishing attacks. However, below discussed are some broadly categorized types of phishing attacks.
1. E-mail Phishing
E-mail phishing is the most common and broadly carried phishing attack by attackers. In e-mail phishing, the attacker tries to mimic the real e-mails of the organizations with unnoticeable changes to trick the users.
Fake domains or substitutions like replacing ‘w’ with ‘vv’ make the e-mail look authenticate; such differences for regular users are difficult to notice.
2. Spear Phishing
Spear phishing is targeted Phishing that targets the specific user or the group of people. Some are similar community based like employees of one organization, so targeting this spear phishing is carried out in which attackers already have the victims’ information like name, job profile, contact details, etc.
In spear, phishing attackers design the e-mails according to the targets, making it easy to trick victims.
3. Whaling
Whaling is similar to spear phishing. It is also a targeted attack, but in whaling, the targets are the high authorized person or senior management of the organization.
In a whaling attack, the common techniques used by the attackers, as we discussed in e-mail phishing, such as using look-alike domains or mimicking the real e-mails, may not work as a victim is a high authorized person. They may not fall for such a trick, so in whaling, attackers craft the mails using personalized information of the target, such as tax returns, lawsuits, family-related, etc.
4. Smishing
In a smishing attack, the attacker uses mobile text communication as a mode of communication to carry out the phishing attack.
The malicious links are sent through the text message and a personalized message that tricks the victim, and the attack is executed.
5. Vishing
Vishing is the kind of phishing attack where the mode of communication is phone calls. The fraud phone calls are carried out where attackers masquerade the authorized person’s identity and make the victim believe it is real communications and attack is executed, or the victim gives out the information.
Most popular vishing attacks nowadays are where attacker scams the people for paying money by making a fraud calls.
6.Watering Hole Phishing
This attack is quite an advanced attack than all the phishing attacks where attackers do not target the victim directly; rather, they compromise or attack the websites or services which victim uses the most, so when the victim uses that service, they fall for the phishing attack that is be implanted by the attacker.
Such attacks are hard to identify and give additional benefits for the attackers as not only targeted users but all those who visit the compromised website get affected by the attack that is just additional victims for the attack executed.
No Phish – Mitigations to avoid Phishing attacks:
- Always check the sender of the mail check for any spoofing or spelling errors in domains.
- Always check for the URLs present inside the mails and open the links only if the e-mails are from trusted sources.
- Use trusted sources only; never give out personal information on any unwanted platforms.
- Never trust suspicious calls.
- Implement multi-factor authentication on services you use for additional security.
Protect your Domain.
As an organization, you need to protect your customers or people from phishing attacks that use your domain for sending Phishing e-mails. Therefore, you need to implement a system that will authenticate the real mails sent from your domain and tell the user if the mail received from your domain is legitimate or the false mail they need to avoid communication with to avoid loss.
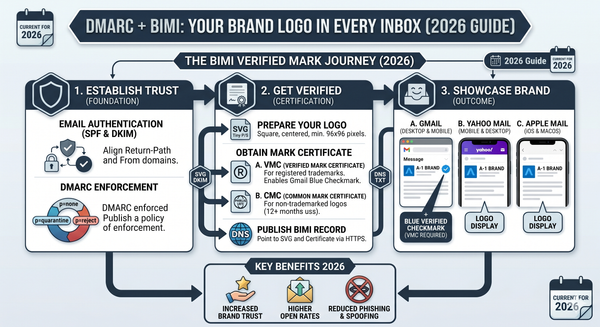
DMARC here comes as a saviour for the organizations to handle these e-mail attacks, so implementing DMARC for your organization’s domain can prevent usage of your domains from sending false e-mails by attackers.
DMARC stands for Domain-Based Message Authentication, Reporting, Conformance. DMARC is an E-mail validation Standard that helps in the prevention of e-mail spoofing.
DMARC works with or builds upon two more E-mail protocols SPF(Sender Policy Framework) and DKIM(DomainKeys Identified E-mail).
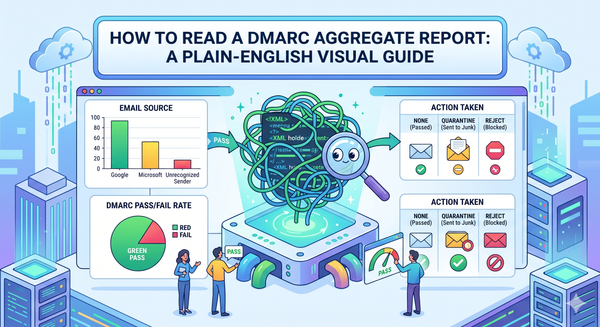
DMARC acts at a gateway or mail server to authenticate e-mail whether it’s from the real source, i.e. the domain entry is present at DNS records by passing it through both SPF and DKIM validation protocols and aligning them if the e-mail gets aligned, then it is verified and sent to receiver otherwise quarantined or gets rejected