Three Musketeers – DKIM, SPF and DMARC

Phishing Attacks: Email is Cybercriminals’ Number One Target
For many of us, the threats are most likely to arrive as emails or attached to emails. Cybercriminals use emails as a bridge to spread malware and infect computers in various ways. Tricking users into clicking malicious links and downloading an attached file that would run the malicious code on user machines is one of the most known.
Did you know that 60% of all worldwide email traffic is marked as SPAM or phishing? That’s a significant percentage. While you’re sending emails, there might be others sending emails on your behalf. They mask their identity by sending it on behalf of your domain. Both emails are delivered to the inbox of the receiver. At this point, the email that the hacker sends is so well-crafted that it looks like a legitimate email from a brand or company the receiver knows. Trusting and assuming the email is authentic, the receiver opens the email and clicks the link without doubting malicious. And, of course, he takes his place among those who fall for the trick; now, he’s going to be taken to a fake website that collects his information.
You may be assuming you already know all this stuff and take your precautions. However, there isn’t a day that passes where scams aren’t in the news one way or another. Phishing scams remain one the most frequent attacks that happen. If you don’t want to become the next victim, you should know how to use the latest weapon in the war against spam.
SPF – The First Musketeer
SPF stands for Sender Policy Framework. It is an email authentication technique that validates an email message sent from an authorized mail server to protect email senders and recipients from spam, spoofing and phishing. It is designed to prevent spammers from sending forged emails from the domain they’re claiming to be. When a spammer attempts to send an email from a faked address, the message will be marked as suspicious and be rejected by the email receiver.
Now, you may wonder how SPF works.
Here are three steps how the process works:
- With SPF, a domain administrator can publish authorized mail servers to send an email from that domain. SPF record is included in an organization’s DNS database, and it is a specially formatted form of DNS TXT record. So, you can specify which IP addresses and hostnames are authorized to send emails from the specific domain in the SPF record.
- When the mail receiver receives an incoming email, it uses the “envelope from” address of the mail (mainly the Return-Path header) to confirm the sending mail server is included in the SPF record comparing the IP address of the sending domain with the authorized IP addresses.
- The mail receiver uses the rules specified in the sending domain’s SPF record to accept or reject the email message.
If you are a company sending commercial emails, you’ll need to have one form or more of email authentication techniques to verify that an email is from your company. Apart from SPF, new email authentication techniques have evolved and lead to DKIM and DMARC. According to some email experts, implementing DKIM and DMARC is necessary to define a complete authentication policy.
However, we should consider SPF as one of the significant steps to improve your deliverability and still plays an essential role in determining whether an email is DMARC Compliant.
DKIM – The Second Musketeer
DKIM stands for Domain Keys Identified Mail. It is an email authentication technique designed to help the receiver make sure that an email is indeed sent and authorized by the owner of that domain. It uses public-key cryptography to sign an email with a private key, showing if an email message is sent from an authorized mail server. Once recipient servers verify that the email is signed with a valid DKIM signature, certainly, the message body and attachments haven’t been modified during transit. So, parts of the email are considered authentic. As the validation is done on a server level, end-users usually cannot see the DKIM signature.
With the DKIM standard, your email deliverability will improve. Along with DMARC and even SPF, using DKIM records will help you prevent malicious emails sent on behalf of your domain and create multiple layers of security for domains sending emails.
DKIM isn’t a required standard. However, your email signed with DKIM look more legitimate to your recipients and, therefore, less likely to go to Spam or Junk folders. Therefore, adding a DKIM record to your DNS is highly recommended whenever possible to authenticate mail from your domain. Implementing DKIM makes it harder to spoof email from domains that use it.
Let’s move on to how DKIM works.
- The outbound mail server sends a message. The server generates a unique DKIM signature header. This header contains information on how the signature is generated.
- Inbound mail server or recipient server receives the message and looks up the sender’s public DKIM key in DNS to verify the signature. The recipient server uses this key to decrypt the Hash value in the header and compare it to the values from the received mail. If they match, the MTA (Mail Transfer Agent) that generates the DKIM signature knows that the DKIM is valid, and the email has not been altered.
DMARC – The Third Musketeer
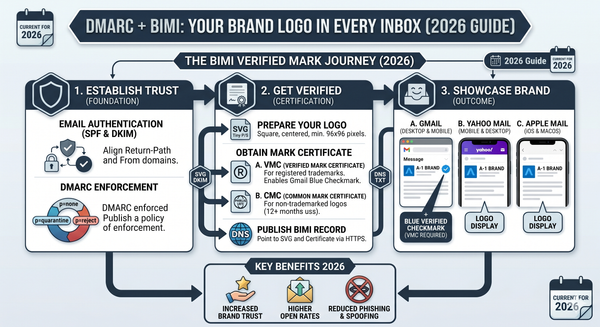
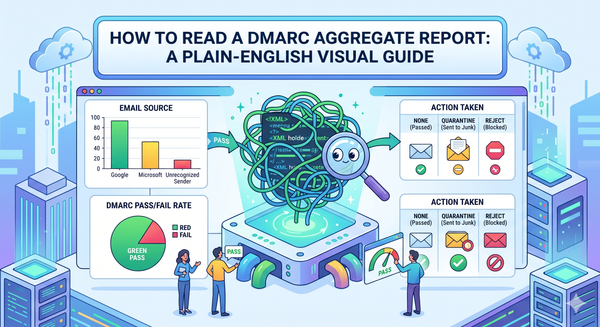
DMARC or Domain-based Message Authentication, Reporting & Conformance is a free and open technical protocol that uses SPF and DKIM mechanisms to determine the authenticity of an email message. DMARC is built upon SPF and DKIM. DMARC brings consistency to how SPF and DKIM technologies are configured. With DMARC in place, large and small domain owners fight against phishing and spoofing. Together the Three Musketeers are considered the best practice to hinder email spoofing and phishing attacks. Without setting up both SPF and DKIM, DMARC does not work. If you apply the process carefully, using the DMARC Analyzer tool, you can receive DMARC reports containing detailed information about who is sending emails on your behalf.
If you’re a business owner, you want to ensure that only your customers can see emails sent by yourself. For this reason, DMARC is a must for domain owners. When you secure your email with DMARC, email receivers will identify the email as legit and originates from you, positively impacting email delivery.
Let’s look at briefly how DMARC works:
- A domain administrator publishes a DMARC DNS Record at their DNS hosting company.
- When an email is sent by someone spoofing the domain, the inbound mail server uses DNS to look up the DMARC policy for the domain in the message’s “From” header.
- The three checked key factors are as follows:
- Does the message have the DKIM signature that validates?
- Does the IP address of the sender match authorized senders in the SPF record?
- Do the headers in the message pass “domain alignment” tests?
- With the SPF and DKIM results on hand, the server is ready to apply the sending domain’s DMARC policy (p=none, p=quarantine, or p=reject)
- The inbound mail server will report the outcome to the sending domain owner, deciding what to do with the message.
In short, originally, SPF and DKIM helped protect your domains from scams. However, it’s not that hard for hackers to bypass these security measures. If you wish to secure your domain and email channel fully, DMARC forms a link between SPF and DKIM. DMARC overcomes the problem by ensuring that the domain seen by the end-user is the same as the one validated by SPF and DKIM.
- SPF verifies that the sending server is authorized to send messages using a domain in the first place.
- DKIM ensures messages remain unchanged in transit between the sending and recipient servers
- DMARC uses SPF and DKIM to identify if a message is legitimate and whether it should be delivered to the recipient or blocked in the first place.