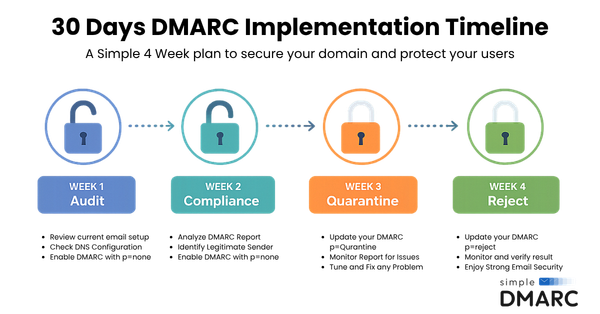
How to Move from p=none to p=reject in 30 Days: The SimpleDMARC Roadmap
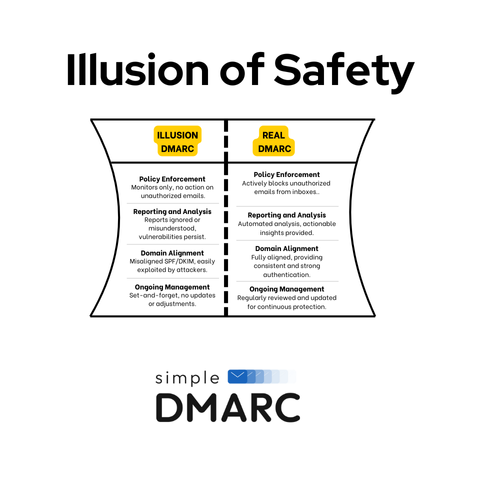
If your domain's DMARC policy is still set to `p=none`, you can see who's attacking you — but you can't stop them.
Gaurav Maniar is the founder of SimpleDMARC and GavBit, specializing in email security, DMARC implementation, and phishing prevention. He develops tools and resources to help organizations protect domains from spoofing and email-based threats.

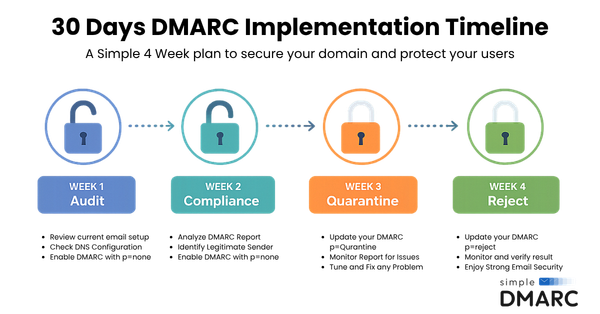
If your domain's DMARC policy is still set to `p=none`, you can see who's attacking you — but you can't stop them.

Picture this: your CEO's email address just sent 50,000 phishing emails to your customers. Except it wasn't actually your CEO. Welcome to the world of domain spoofing, where anyone can pretend to be anyone else — unless you've got DMARC, BIMI, and VMC working for you.
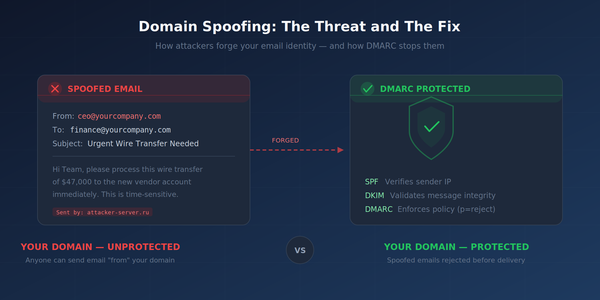
A straightforward guide to understanding domain spoofing attacks, why your business domain is a target, and what you can do about it today.

Week 1 of 8 – Understand the Threat Before It Hits You In a world where cyber threats evolve faster than ever, phishing remains the #1 entry point for data breaches and ransomware attacks. If you've ever received a suspicious email asking you to "verify your account"

Introduction Black-friday that’s an excellent shopping event famous for great deals and shopping revival is also the best time for online scammers to swoop in. As the usually shopping shifted to online, the channels through which scammers can work have increased tremendously. This article explores and explains different Black
Phishing
Phishing vs. spear phishing—understand their differences. Explore how each threat operates and get tips on staying secure from cybercriminals targeting your data.
Phishing attack
Discover how a single negative trigger can outweigh five positive experiences in phishing attacks. Learn the psychological tactics used by cybercriminals to exploit human vulnerabilities and how to protect yourself.
Introduction The Growing Threat of Phishing Phishing attacks have become a persistent menace in today's digital landscape, with cybercriminals refining their tactics to deceive even the most cautious users. From cleverly disguised emails to sophisticated impersonation schemes, phishing is an annoyance and a significant security threat that can

Phishing awareness
Introduction Phishing scams are fraudulent attempts to obtain sensitive information by masquerading as a trustworthy entity in electronic communications. With cybercriminals becoming increasingly sophisticated, it's crucial to recognize and avoid phishing emails. We will provide five powerful tips to help identify phishing scams and protect yourself from threats.

Discover how to protect your organization from Business Email Compromise (BEC) with recent attack examples, the role of AI and GPT in increasing risks, and how DMARC can prevent BEC. Learn key strategies to safeguard your email security.

Phishing attack
Introduction Phishing scams are deceptive attempts to obtain sensitive information by acting as trustworthy entities in electronic communications. These scams pose considerable risks to individuals and organizations, leading to data breaches, financial losses, and identity theft. As we progress into 2024, the sophistication of phishing attacks continues to evolve, making

Phishing attack
Discover expert strategies to shield your small or medium-sized business (SMB) from phishing attacks. This guide offers actionable insights on enhancing cybersecurity, training employees, and implementing advanced protection measures to secure your digital assets against sophisticated threats.