DMARC vs. SPF vs. DKIM: Understanding the Differences
In email authentication, three essential protocols are crucial in ensuring the security and authenticity of email communications: DMARC, SPF, and DKIM. These three acronyms may seem daunting, but understanding their differences is essential for anyone concerned about email security. In this article, we will break down DMARC, SPF, and DKIM, exploring their purposes and how they work to protect your inbox from phishing attacks and email spoofing.
1. SPF (Sender Policy Framework)
SPF, which stands for Sender Policy Framework, is an email authentication protocol to detect email spoofing. Email spoofing occurs when a malicious sender forges the sender's address to make it appear that the email is from a trusted source. SPF helps prevent this by allowing domain owners to specify which mail servers are authorized to send emails on behalf of their domain.
How SPF Works:
When an email is sent, the receiving mail server checks the SPF record of the sender's domain. The SPF record contains a list of authorized mail servers. The email is legitimate if the sender's mail server matches one of the authorized servers listed in the SPF record. Otherwise, it may be marked as potentially fraudulent.
2. DKIM (DomainKeys Identified Mail)
DKIM, which stands for DomainKeys Identified Mail, is another email authentication protocol that verifies the integrity of the email's content and the sender's authenticity. Unlike SPF, DKIM focuses not on the sender's server but the email's content.
How DKIM Works:
When an email is sent, the sender's mail server adds a digital signature to the email's header using the private key associated with the sender's domain. The receiving mail server then verifies the signature using the public key published in the sender's domain's DNS records. The email is considered genuine if the signature is valid and the message has not been altered in transit.
3. DMARC (Domain-based Message Authentication, Reporting, and Conformance)
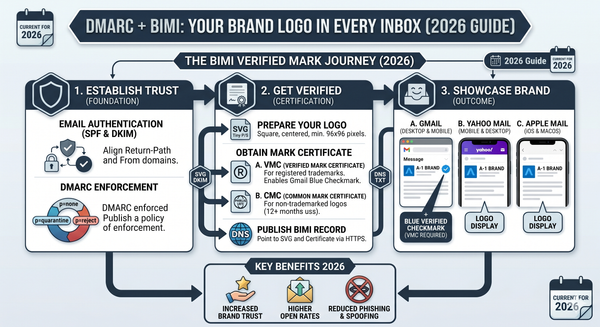
DMARC, short for Domain-based Message Authentication, Reporting, and Conformance, is a comprehensive email authentication protocol that builds upon SPF and DKIM. It adds a layer of protection by allowing domain owners to instruct receiving mail servers on handling emails that fail SPF or DKIM checks.
How DMARC Works:
When a receiving mail server encounters an email claiming to be from a domain that has implemented DMARC, it first checks for SPF and DKIM authentication. If either SPF or DKIM passes, the email is considered legitimate. However, if both SPF and DKIM fail, the DMARC policy comes into play. The DMARC policy instructs the receiving mail server whether to quarantine, reject, or accept the email, depending on the domain owner's configuration.
Conclusion
In summary, SPF, DKIM, and DMARC are all crucial components of modern email authentication. SPF helps identify authorized mail servers, DKIM verifies the integrity of the email's content and the sender's identity, and DMARC provides instructions on handling emails that fail SPF or DKIM checks. Together, these protocols combat phishing attempts, email spoofing, and other email-based security threats, providing a safer and more secure email experience for users and organizations alike. Implementing these authentication protocols is essential for protecting your domain reputation and ensuring that your emails reach their intended recipients without falling into the traps of cyber criminals.
FAQs
1. Should I implement all three protocols (SPF, DKIM, and DMARC)?
While implementing all three protocols provides the highest level of email security, even implementing just one (SPF or DKIM) can significantly reduce the risk of email spoofing and phishing attacks.
2. How can I set up SPF, DKIM, and DMARC for my domain?
Setting up SPF, DKIM, and DMARC requires modifying your domain's DNS records. Many email service providers offer step-by-step guides to help you configure these protocols correctly.
3. Can implementing DMARC cause legitimate emails to be rejected?
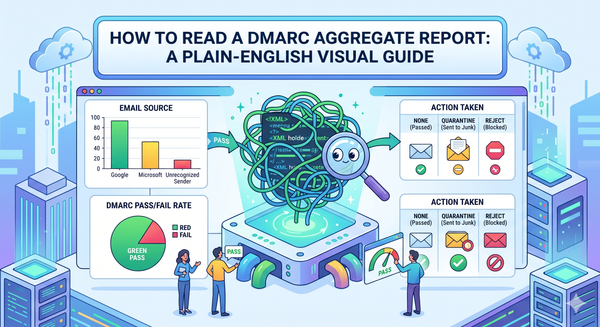
Yes, if not configured correctly, DMARC has the potential to reject legitimate emails. Monitoring DMARC reports and adjusting your policy accordingly is essential to avoid false positives.
4. Are these protocols 100% foolproof against email threats?
While SPF, DKIM, and DMARC significantly enhance email security, no solution is foolproof. It is essential to stay vigilant and follow other email security best practices to protect against evolving threats.
5. Is email authentication only necessary for businesses?
No, email authentication is beneficial for both businesses and individual users. Cybercriminals target all types of email accounts, and implementing these protocols can protect your personal and professional communications.